Cryptography (nonfiction): Difference between revisions
No edit summary |
|||
| Line 1: | Line 1: | ||
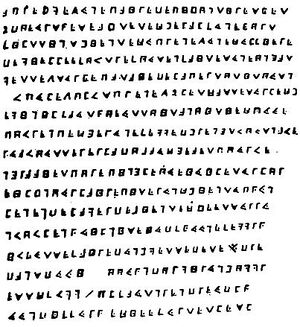
'''Cryptography''' (or '''cryptology'''; from Greek ''κρυπτός'' kryptós, "hidden, secret"; and ''γράφειν'' graphein, "writing", or ''-λογία'' -logia, "study", respectively) is the practice and study of techniques for secure communication in the presence of third parties (called adversaries). | [[File:Crypto_de_la_buse.jpg|thumb|"Cryptogramme du Forban" trouvé à l'île Mahé. C'est un message chiffré, lancé dans la foule par le pirate La Buse montant au supplice, qui révélerait l'emplacement de ses trésors (Bibliothèque Nationale).]]'''Cryptography''' (or '''cryptology'''; from Greek ''κρυπτός'' kryptós, "hidden, secret"; and ''γράφειν'' graphein, "writing", or ''-λογία'' -logia, "study", respectively) is the practice and study of techniques for secure communication in the presence of third parties (called adversaries). | ||
More generally, it is about constructing and analyzing protocols that block adversaries. | More generally, it is about constructing and analyzing protocols that block adversaries. | ||
Modern cryptography exists at the intersection of the disciplines of [[mathematics (nonfiction)|mathematics]], computer science, and electrical engineering. | |||
Modern cryptography exists at the intersection of the disciplines of [[mathematics (nonfiction)]], computer science, and electrical engineering. | |||
Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense. | |||
Cryptography prior to the modern age was effectively synonymous with | |||
The originator of an encrypted message shared the decoding technique needed to recover the original information only with intended recipients, thereby precluding unwanted persons from doing the same. | The originator of an encrypted message shared the decoding technique needed to recover the original information only with intended recipients, thereby precluding unwanted persons from doing the same. | ||
Since World War I and the advent of the [[computer (nonfiction)|computer]], the methods used to carry out cryptology have become increasingly complex and its application more widespread. | |||
== Fiction cross-reference == | |||
* [[Cryptographic numen]] | |||
* [[Casio + N = CasiNo]] | |||
== Nonfiction cross-reference == | == Nonfiction cross-reference == | ||
| Line 35: | Line 21: | ||
* [[Information security (nonfiction)]] | * [[Information security (nonfiction)]] | ||
* [[Mathematics (nonfiction)]] | * [[Mathematics (nonfiction)]] | ||
== External links == | == External links == | ||
Revision as of 05:32, 11 June 2016
Cryptography (or cryptology; from Greek κρυπτός kryptós, "hidden, secret"; and γράφειν graphein, "writing", or -λογία -logia, "study", respectively) is the practice and study of techniques for secure communication in the presence of third parties (called adversaries).
More generally, it is about constructing and analyzing protocols that block adversaries.
Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, and electrical engineering.
Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense.
The originator of an encrypted message shared the decoding technique needed to recover the original information only with intended recipients, thereby precluding unwanted persons from doing the same.
Since World War I and the advent of the computer, the methods used to carry out cryptology have become increasingly complex and its application more widespread.
Fiction cross-reference
Nonfiction cross-reference
External links
- Cryptography @ Wikipedia
- Cryptography @ Wikipedia